CROT4D is a versatile framework/platform/system renowned for its robustness/efficiency/versatility. This guide/tutorial/handbook aims to demystify/illuminate/explain the fundamentals of CROT4D, empowering beginners/novices/newcomers with the knowledge to navigate/explore/utilize its features effectively.
- Firstly/Initially/First and foremost, we'll delve into the core concepts of CROT4D, outlining its architecture/structure/design.
- Next/Subsequently/Following this, you'll gainhands-on experience with essential/fundamental/basic tasks, such as/including/like installation/configuration/setup and development/implementation/creation.
- Furthermore/Moreover/Additionally, we'll explore advanced topics, enabling/facilitating/permitting you to optimize/maximize/enhance your CROT4D workflow/process/operations.
Whether you're a student/enthusiast/developer eager to master/learn/understand CROT4D, this guide will serve as an invaluable resource/tool/companion throughout your learning/exploration/journey.
Unleashing the Power of CROT4D for Security Research
CROT4D has emerged as a potent tool in the realm of security research. Its ability to analyze complex security protocols and identify vulnerabilities makes it an invaluable asset for researchers seeking to enhance system protection. By leveraging CROT4D's capabilities, researchers can uncover hidden threats and develop effective mitigation strategies.
One of the key advantages of CROT4D is its sophisticated algorithms, which enable it to detect subtle anomalies and patterns that may indicate a security breach. This accuracy allows researchers to focus their efforts on the most critical vulnerabilities, maximizing the impact of their investigations.
Furthermore, CROT4D's transparent nature fosters collaboration and knowledge sharing within the security community. Researchers can freely utilize the tool, modify it to suit their specific needs, and contribute back to its development. This collaborative environment accelerates innovation and drives the advancement of security research as a whole.
Leveraging Advanced CROT4D Techniques for Penetration Testing
Penetration testers constantly seek innovative methods to circumvent security measures and uncover vulnerabilities. Among these techniques, CROT4D has emerged as a powerful framework for simulating real-world attacks. This article delves into advanced CROT4D methodologies, empowering ethical hackers to conduct more comprehensive and effective assessments. We'll explore sophisticated strategies like blind injection, credential harvesting, and network reconnaissance, showcasing how these can be leveraged to gain deeper insights into system weaknesses. By mastering these advanced methods, security professionals can significantly enhance their penetration testing capabilities, identifying critical vulnerabilities before malicious actors exploit them.
Dominating CROT4D Scripting for Automated Tasks
Unlock the potential of optimization with CROT4D scripting. This powerful language empowers you to build intricate scripts that process complex tasks with ease. From repetitive operations to intricate data handling, CROT4D provides a versatile toolkit for developers and professionals. By mastering its core concepts, you can significantly enhance your productivity and accomplish remarkable results.
- Dive into the fundamentals of CROT4D syntax and organization.
- Utilize its powerful tools for data retrieval.
- Automate repetitive tasks with powerful scripts.
Embrace CROT4D scripting into your workflow and enjoy the transformative power of automation.
CROT4D in Action: Real-World Use Cases
CROT4D's robust capabilities have found widespread application across a variety of industries. In the industrial sector, CROT4D is employed for risk assessment, helping organizations mitigate potential losses. Furthermore, in the pharmaceutical field, CROT4D streamlines patient data management, facilitating treatment decisions.
- In the production domain, CROT4D automates operations, enhancing output.
- Additionally, in development, CROT4D enables knowledge discovery, leading to innovations in various areas.
These are just a few examples of how CROT4D is revolutionizing industries and driving progress in the real world. Its adaptable nature allows it to be integrated into diverse environments, making it a truly valuable tool for organizations seeking to optimize their performance.
Creating Secure Applications with CROT4D
CROT4D provides a robust and thorough framework for constructing secure applications. By leveraging its powerful features, developers can eliminate security vulnerabilities and provide the confidentiality of sensitive data. CROT4D's flexible architecture allows seamless deployment with existing systems, facilitating it an ideal choice for organizations desiring to strengthen their security posture.
- Additionally, CROT4D's intuitive interface expedites the development process, enabling developers to focus on developing secure and dependable applications.
- Moreover, CROT4D's vibrant community of developers provides valuable support and tools to strengthen the development experience.
Exploring this CROT4D Ecosystem
Delving into the intricacies of the CROT4D ecosystem unveils a robust landscape of resources. Users can utilize a variety of capabilities to build innovative solutions. From advanced modules to detailed documentation, the ecosystem offers a favorable environment for exploration.
- Additionally, the CROT4D community is renowned for its collaboration, fostering a culture of knowledge sharing.
- This collective efforts contribute in a constantly progressing ecosystem that remains at the leading edge of technology.
CROT4D vs. Other Frameworks: A Comparative Analysis
When evaluating deep learning frameworks for demanding tasks, CROT4D emerges as a compelling option. Compared to established frameworks like TensorFlow and PyTorch, CROT4D demonstrates several distinct features.
- For starters, CROT4D's design is optimized for concurrent execution, enabling it to handle large volumes of data with improved performance.
- Secondly, CROT4D's modular design allows developers to tailor the framework to specific needs.
- Finally, CROT4D's vibrant ecosystem provides valuable assistance for developers.
However, it's important to assess that CROT4D is a relatively new framework, and its popularity is still expanding.
Transforming Trends in CROT4D: Forecasts for the Next Decade
CROT4D, a rapidly evolving field/discipline/sector, is poised for significant growth/expansion/advancement. Key trends/developments/movements shaping its destiny/course/trajectory include blockchain integration/AI-driven solutions/quantum computing applications. These technologies/innovations/breakthroughs are revolutionizing/disrupting/transforming traditional paradigms, creating new opportunities/possibilities/avenues for collaboration/innovation/progress. As we venture/embark/journey into the future/coming years/next era, CROT4D is expected to become/evolve into/shape a powerful/influential/pivotal force in global/worldwide/international affairs/industry/society.
- Specific trend 1 with detailed explanation
- Specific trend 2 with detailed explanation
- Specific trend 3 with detailed explanation
Top 10 CROT4D Security Tools
In the ever-evolving landscape of cybersecurity, staying ahead of threats is paramount. CROT4D security tools play a vital role in this endeavor, providing comprehensive protection against malicious actors. Selecting the right set of tools can be a daunting task, so we've compiled a list of the top 10 CROT4D security tools to empower your defenses.
- Network Security Appliance: A fundamental layer of security that filters unauthorized access to your network.
- Endpoint Protection: Shields your devices from malicious software and viruses.
- Intrusion Detection System (IDS): Monitors suspicious activities within your network for potential breaches.
- Data Encryption: Secures your internet traffic, safeguarding sensitive data during transmission.
- Unified Threat Management (UTM): A comprehensive solution that integrates multiple security features for robust protection.
Crafting Effective CROT4D Malwares
Delving into the shadowy realm of malware creation requires a meticulous understanding of its inner workings. CROT4D, a widespread strain of malware, poses a significant threat to systems. Crafting effective CROT4D malware necessitates utilizing vulnerabilities in operating systems, coupled with refinedevasion techniques to bypass safeguards.
One critical aspect of CROT4D malware development is the method of infection.
Employing methods such as phishing campaigns allows attackers to propagate the malware to unsuspecting victims. Once infiltrated, CROT4D can take control of infected systems.
- Cybercriminals
- Continuously evolve their malware tactics to stay ahead of security measures.
Staying aware of the latest CROT4D threats and implementing robust security protocols is paramount to mitigating the risks associated with this dangerous malware.
Comprehending CROT4D Network Protocols
CROT4D network protocols regulate the flow of information across a distributed network. These protocols establish the guidelines for connectivity, ensuring efficient data movement. By implementing CROT4D protocols, systems can attain high levels of speed, while maintaining data protection. A key characteristic of CROT4D is its flexibility, allowing networks to expand in size and sophistication without compromising efficiency.
Deciphering CROT4D Code Obfuscation
CROT4D is a notorious cybersecurity that utilizes sophisticated code obfuscation techniques to evade detection by security software. Deciphering this code presents a significant challenge for analysts, requiring in-depth knowledge of programming languages and reverse engineering methodologies. By analyzing the structure, syntax, and control flow of the obfuscated code, researchers can gradually decode its underlying functionality and identify potential vulnerabilities.
- One common strategy employed by CROT4D is the use of character modulation, where critical data elements are converted into unreadable formats.
- Another prevalent tactic involves concealing code within audio files, making it difficult to detect through traditional scanning methods.
The ever-evolving nature of CROT4D necessitates a proactive approach to threat intelligence and defense. By staying informed about the latest variants of this malware and implementing robust security controls, organizations can mitigate the risk of infection and protect their valuable assets.
Debugging CROT4D Applications: Expert Strategies
For seasoned CROT4D developers, debugging can often feel like navigating a labyrinth. While standard techniques may provide some insight, mastering in-depth debugging strategies is crucial for tackling complex issues. This involves leveraging specialized tools and understanding the intricacies of the underlying mechanisms in CROT4D. One powerful approach is to employ a iterative debugging process, meticulously examining each section of code. Another essential technique is to utilize trace statements to gain a clearer understanding of program execution flow and identify potential fault points.
- Examining memory allocations
- Profiling CPU utilization
- Employing breakpoints
By combining these effective debugging techniques, advanced CROT4D users can efficiently resolve even the most challenging issues, ultimately enhancing the stability and performance of their applications.
Securing Your Systems Against CROT4D Attacks
CROT4D is a malicious cyber threat that can exploit vulnerabilities in your systems to acquire sensitive data. To effectively protect yourself against CROT4D attacks, it's crucial to implement a multi-layered security strategy. Start by ensuring your software is current. Regularly refresh your operating systems and applications to minimize the risk of exploitation.
- Secondly, install robust firewall systems to filter unauthorized access to your network.
- Furthermore, consider using intrusion detection and prevention systems (IDPS) to track network traffic for suspicious activity and automatically respond to potential threats.
Train your employees about the dangers of CROT4D attacks and security measures to click here mitigate falling victim to these attacks. Regularly execute security awareness training to keep your team informed about the latest threats and how to defend themselves.
Ethical Hacking with CROT4D: A Vulnerable Approach
The realm of cybersecurity is constantly evolving, demanding innovative strategies to combat ever-growing threats. Ethical hacking, a practice often referred as penetration testing, plays a crucial role in identifying vulnerabilities before malicious actors exploit them. CROT4D, a versatile platform, emerges as a powerful instrument in the hands of responsible security professionals. By employing ethical hacking methods with CROT4D, organizations can efficiently strengthen their defenses and mitigate potential breaches.
- Employing CROT4D's comprehensive features, ethical hackers can simulate real-world attacks, revealing hidden weaknesses in network infrastructure, applications, and systems. This allows for the adoption of targeted patches to address vulnerabilities before they can be exploited.
- Moreover, CROT4D's accessible interface makes it suitable for both novice and experienced security practitioners. Its modular design allows for tailoring to specific testing scenarios, ensuring a thorough and relevant assessment.
- Consequently, ethical hacking with CROT4D empowers organizations to take a proactive stance against cyber threats. By embracing this responsible approach, businesses can build robust security posture, safeguard sensitive data, and maintain the assurance of their stakeholders.
Documentation and Resources for CROT4D
Exploring the world of CROT4D can be a rewarding journey. To help you navigate its complexities and unlock its potential, we've compiled a comprehensive set of documentation and tools. Whether you're just starting out or an experienced developer, you'll find valuable information to enhance your CROT4D endeavors.
- Browse our official website for detailed explanations on core concepts, functionalities, and advanced capabilities.
- Immerse into our online discussions to connect with other CROT4D enthusiasts, share your experiences, and seek guidance.
- Leverage the curated repository of open-source implementations to learn from real-world CROT4D applications.
Remain up-to-date with the latest releases by subscribing our official blog.
The Dark Side of CROT4D: Malicious Applications
While CROT4D presents itself as a powerful tool for development and analysis, its open-source nature unfortunately makes it susceptible to misuse by malicious actors. These bad actors leverage CROT4D's capabilities to construct devious applications designed to steal sensitive information, compromise systems, or spread ransomware. Law enforcement agencies areconstantly working to mitigate these threats and educate developers on the risks of CROT4D misuse.
Scenarios of malicious applications built with CROT4D include:
- Trojan horses that encrypt files for financial gain.
- Monitoring tools that steal passwords.
- Botnets that can be used to launch large-scale cyber assaults.
Analyzing Exploits within CROT4D Framework
Delving into the realm of offensive operations, we encounter the intricate framework known as CROT4D. This complex system has demonstrated its potency in various operations. Examining specific instances of CROT4D exploitation provides valuable understanding into its capabilities and flaws.
- One notable case involves the infiltration of a critical infrastructure where CROT4D was deployed to exfiltrate confidential information.
- Furthermore, investigations have uncovered the use of CROT4D in launching ransomware attacks. These operations have had significant impacts on individuals worldwide.
Analyzing these real-world examples, security researchers can gain insights to mitigate the threats posed by CROT4D. Comprehending its functionalities and strategies is crucial for developing effective security solutions.
Exploring the Legal Consequences of Utilizing CROT4D
Utilizing CROT4D raises a number of significant legal concerns. Primarily, there is the matter of copyright as content generated by CROT4D may not always be clearly owned by the user who provided it. Additionally, the possibility of exploitation of CROT4D for illegal activities is a pressing issue that demands careful legal analysis. Governments and lawmakers are continuously grappling with how to best manage these challenges , and the legal landscape surrounding CROT4D is likely to evolve progressively in the forthcoming years.
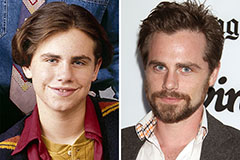 Rider Strong Then & Now!
Rider Strong Then & Now! Alisan Porter Then & Now!
Alisan Porter Then & Now! Robbie Rist Then & Now!
Robbie Rist Then & Now! Erika Eleniak Then & Now!
Erika Eleniak Then & Now! Kerri Strug Then & Now!
Kerri Strug Then & Now!